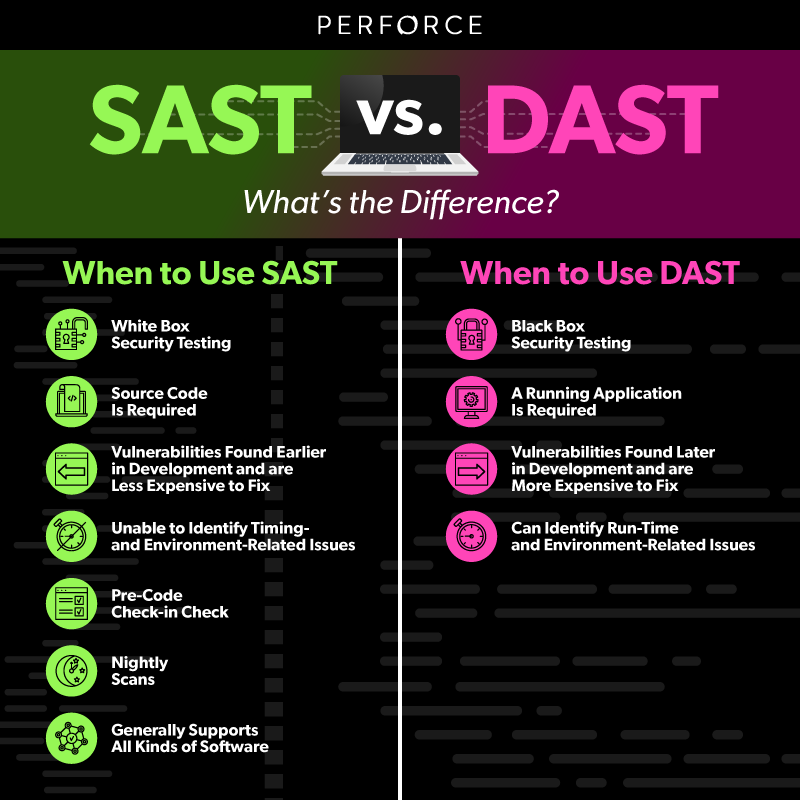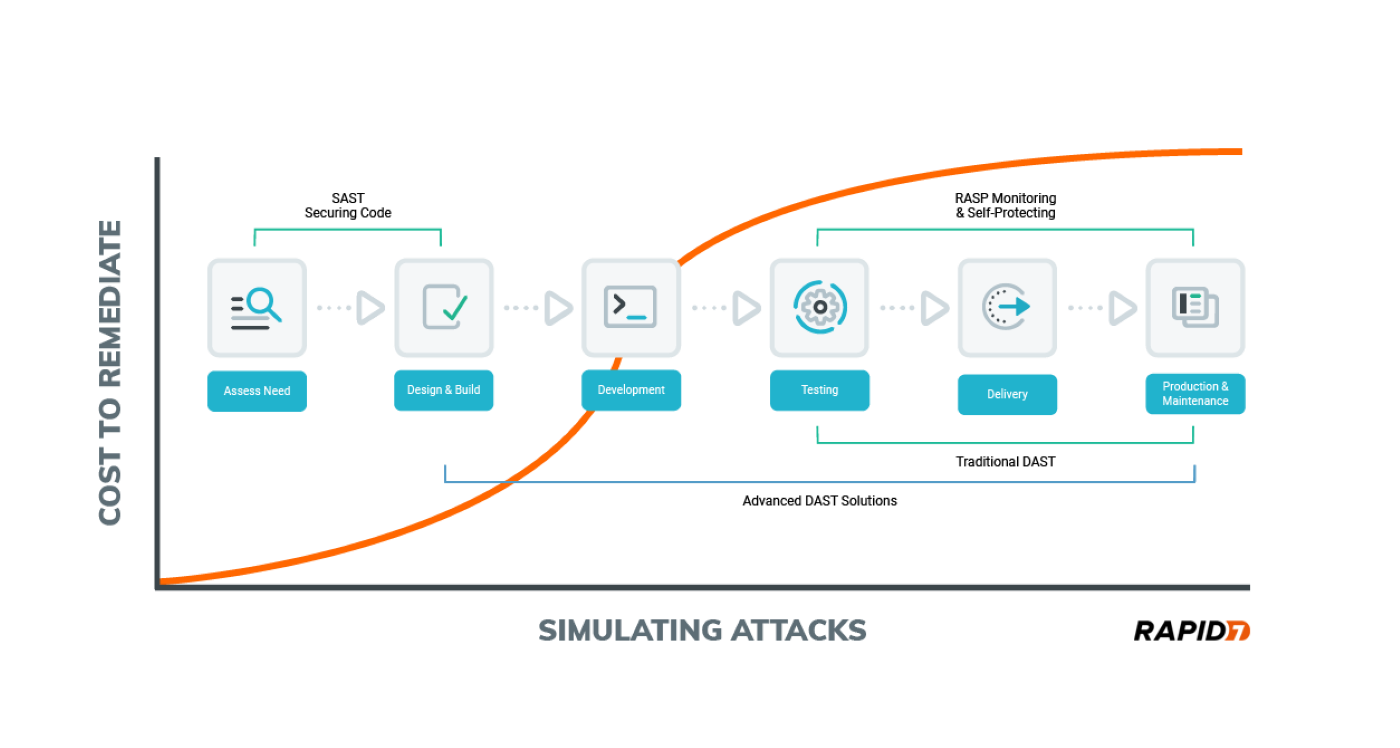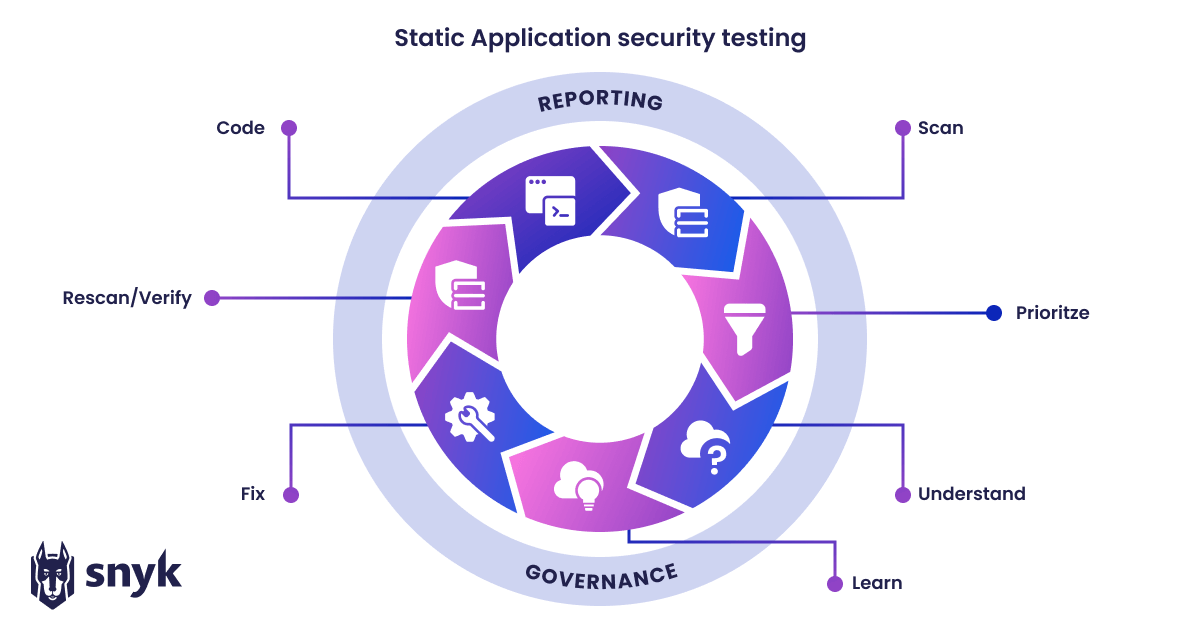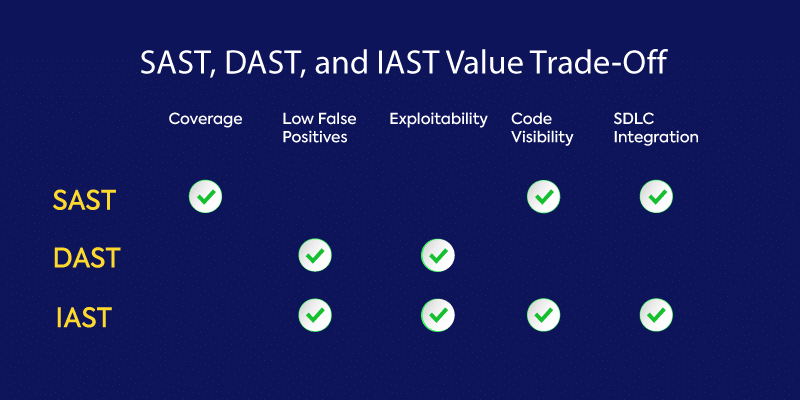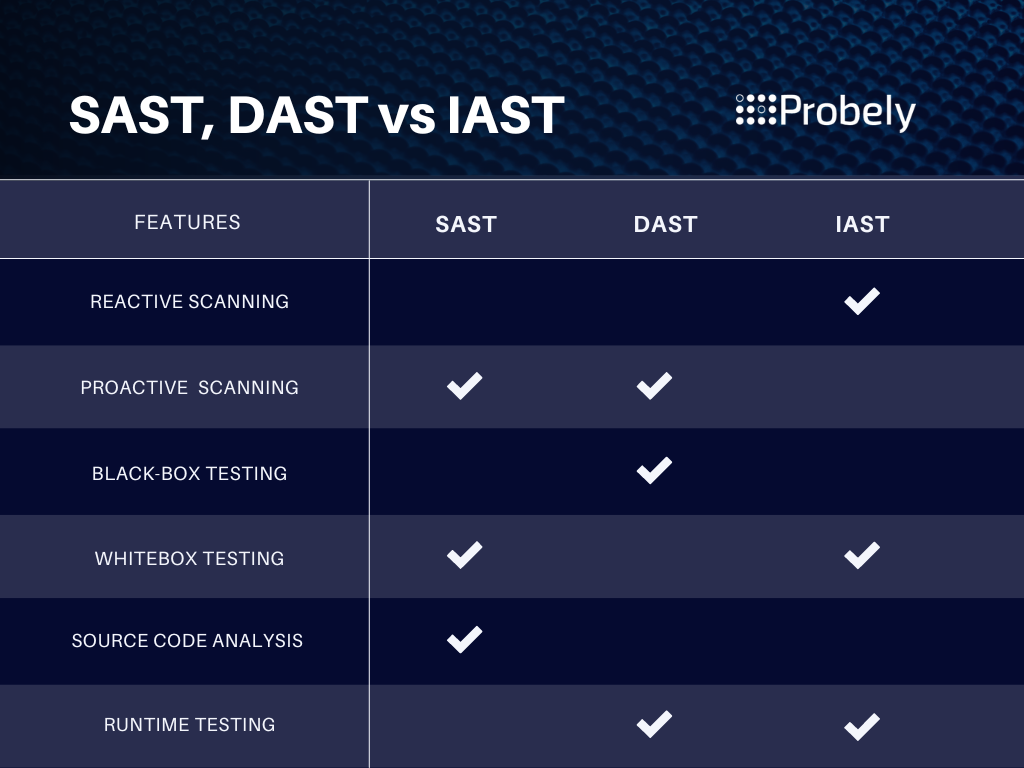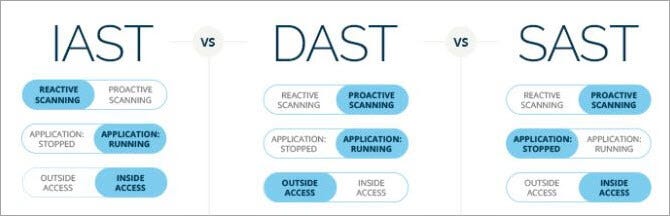
Ensuring Robust Application Security: Exploring SAST, DAST, and IAST for Comprehensive Protection | by Ranjan kumar Singh | Medium

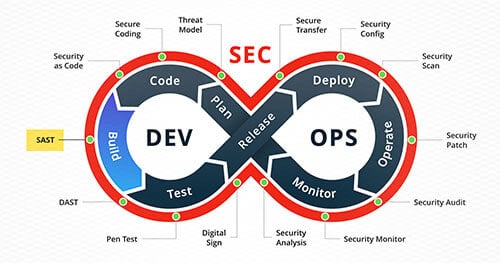
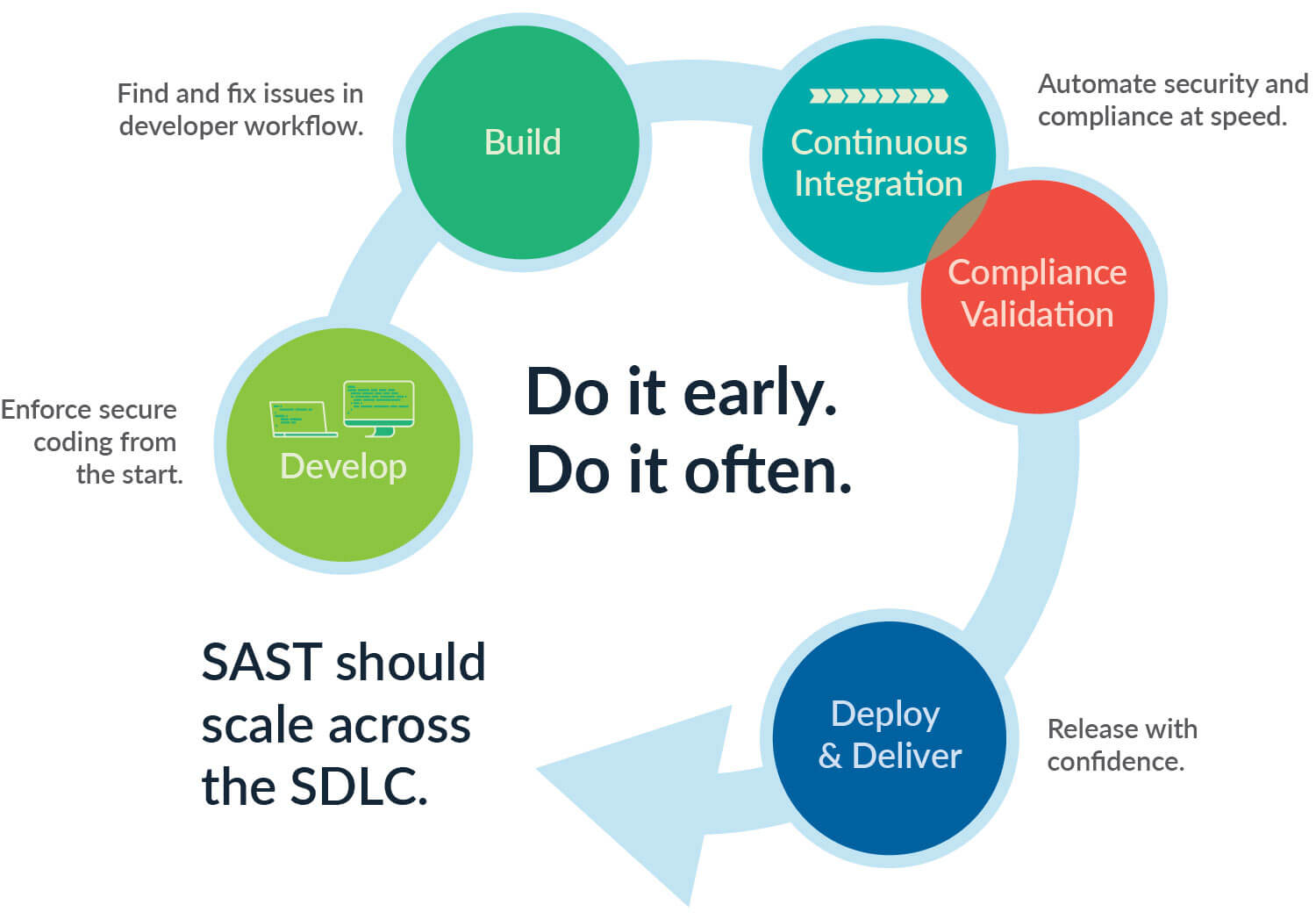
Software Development Lifecycle (SDLC), DevSecOps, SAST, DAST And IAST Concepts | by Ismail Tasdelen | InfoSec Write-ups